The USBKill V4 has an internal battery to deliver "offline attacks" - requiring no power from the host device. As such, USB-C and Lightning / iPhone authentication mechanisms can be completely bypassed.
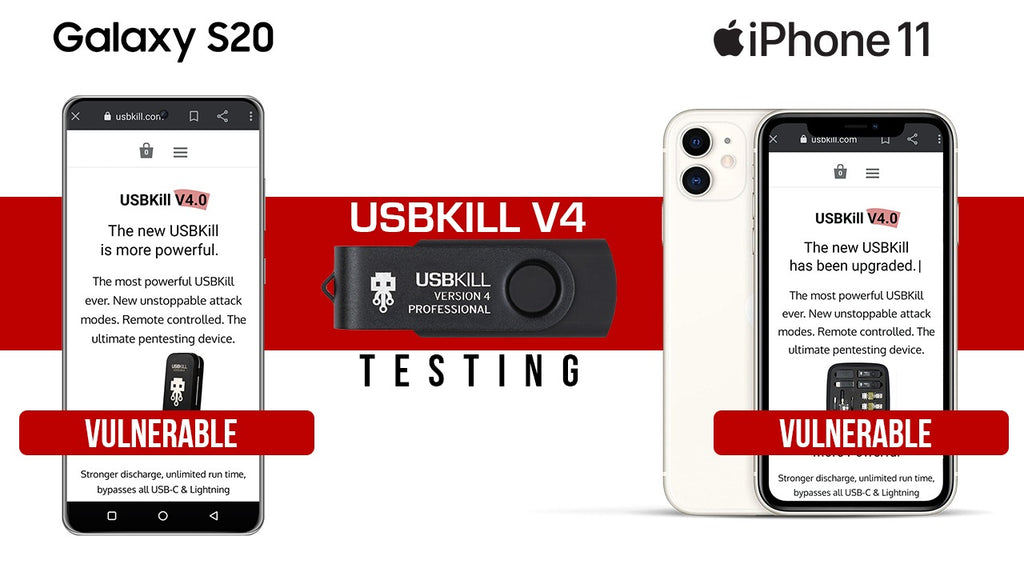
To demonstrate this functionality, we put the USBKill V4 Professional against the current flagship mobile devices: the iPhone 11 and Samsung S20.
We used the V4 Professional teamed with the USB-C and Lightning adaptors, wirelessly configured with smartphone trigger to send continuous pulses.
As you can see below, both devices are vulnerable. The S20 was instantly disabled - the iPhone provides substantial resistance, but eventually fell into an unrecoverable bootloop.
The USBKill V4 Pro Kit is available now.